Computer Tear Apart, Study, and Deeestroy Activity
Author: lskramer
Author: lskramer
So that my students could understand the hardware and data systems driving cyber space and Information and Communications Technology I organized a two session activity.
The first day the class was given the opportunity to examine and tear apart the insides of laptops and desktop computers. We chose several generations so they could appreciate the differences generational changes make for example better optical and solid state hard drives.
I set up three of my “legacy” Mac computers so the students could see the amazing and blazing fast changes that have taken place in the size, weight, and functions of these machines. There was no Wi-Fi or wireless card only various generations of modems or hard wire Ethernet connections. There were floppy drives, a swappable DVD/CD driver in the most recent of these, very low data storage capacity, and incredibly slow processors (chips).
The middle one also had an interesting historic marker. Several of the software applications had freaked out because of Y2K the moment when 1900’s ended and the 2000’s began. As you may remember, computers could not figure out want to do with their time stamp when 1999 suddenly ended January 1, 2000. So several of the software tools just freaked out and put a random date, 1904, as to when they were last opened. I think that’s a nice historic relic from the cyber domain!
Some of my students, tech assistant Calvin Kranig, and David Hemken, the Political Science department tech support “guru,” brought entire machines as well as parts to be examined (carefully because these innards actually can “bite!”)
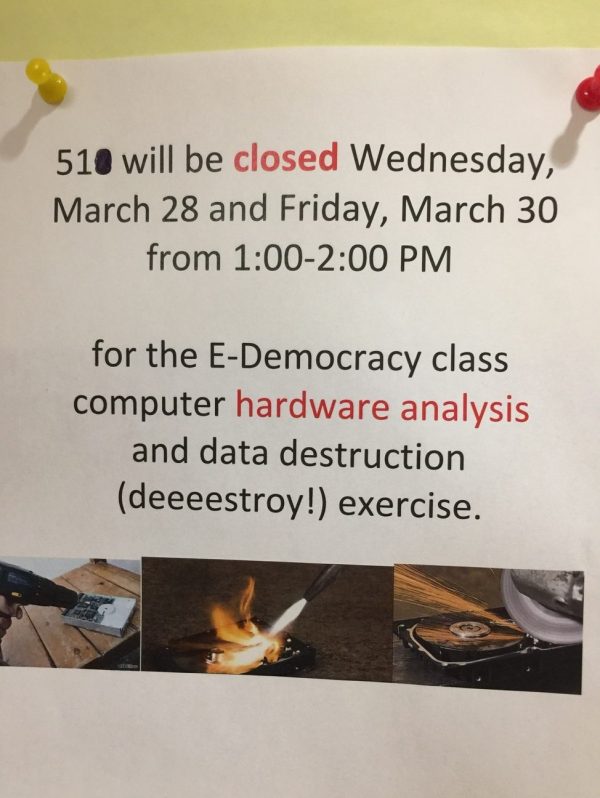
On the second day, Friday, the class learned how to DEEESTROY data on their hard drives through various methods depending on the age of the device. Magnetic wiping, drilling, fire, water, and military grade wiping software were discussed or demonstrated.
I think it was a valuable lesson and experience for my students to understand the complexity as well as the risk vectors we face in these marvelous but very dangerous devices.
Steffen Schmidt